SSO with Entra ID
Configure single sign-on (SSO) with Microsoft Entra ID as an Identity Provider.
Tip
To request an SSO setup for your workspace, please submit a ticket to LeanIX Support.
This document provides guidance on configuring SSO with Entra ID as an Identity Provider (IdP). Before you start, learn more about the configuration process in SSO Configuration Process.
To learn how to add a non-gallery application in Entra ID, please refer to the Entra ID documentation.
Note
We do not support the single sign-out protocol for Entra ID.
Initial Configuration
SAML Settings
Please ensure that the settings are configured according to the example below:
- Identifier (Entity ID):
https://{SUBDOMAIN}.leanix.net/Shibboleth.sso - Reply URL:
https://{SUBDOMAIN}.leanix.net/Shibboleth.sso/SAML2/POST
Note
Replace
{SUBDOMAIN}in the URLs with your value. You can use your company name as the subdomain, so the base URL will appear as follows:https://your-company.leanix.net.
SAML Token Attribute Configuration
When using SAML login with Microsoft Entra, you need to pass a user's first name, last name, email, and role as described in the Single sign-on (SSO) documentation page. These values are defined as SAML Token Attributes in the Relying Party Trust.
In order to properly configure the attribute mapping, custom claim rules need to be configured. The following example rules help to configure your Microsoft Entra federation with LeanIX.
Follow these steps:
-
Configure additional claims using the following values.
Claim Name Type Value firstnameSAML user.givennamelastnameSAML user.surnamemailSAML user.mailroleSAML user.assignedrolesuidSAML user.userprincipalnameThe following image shows the target values that you need to configure. When you open the configuration page, it may show different values. For example, the first claim in the Additional claims table is initially set to
givenname, but you need to change it tofirstname.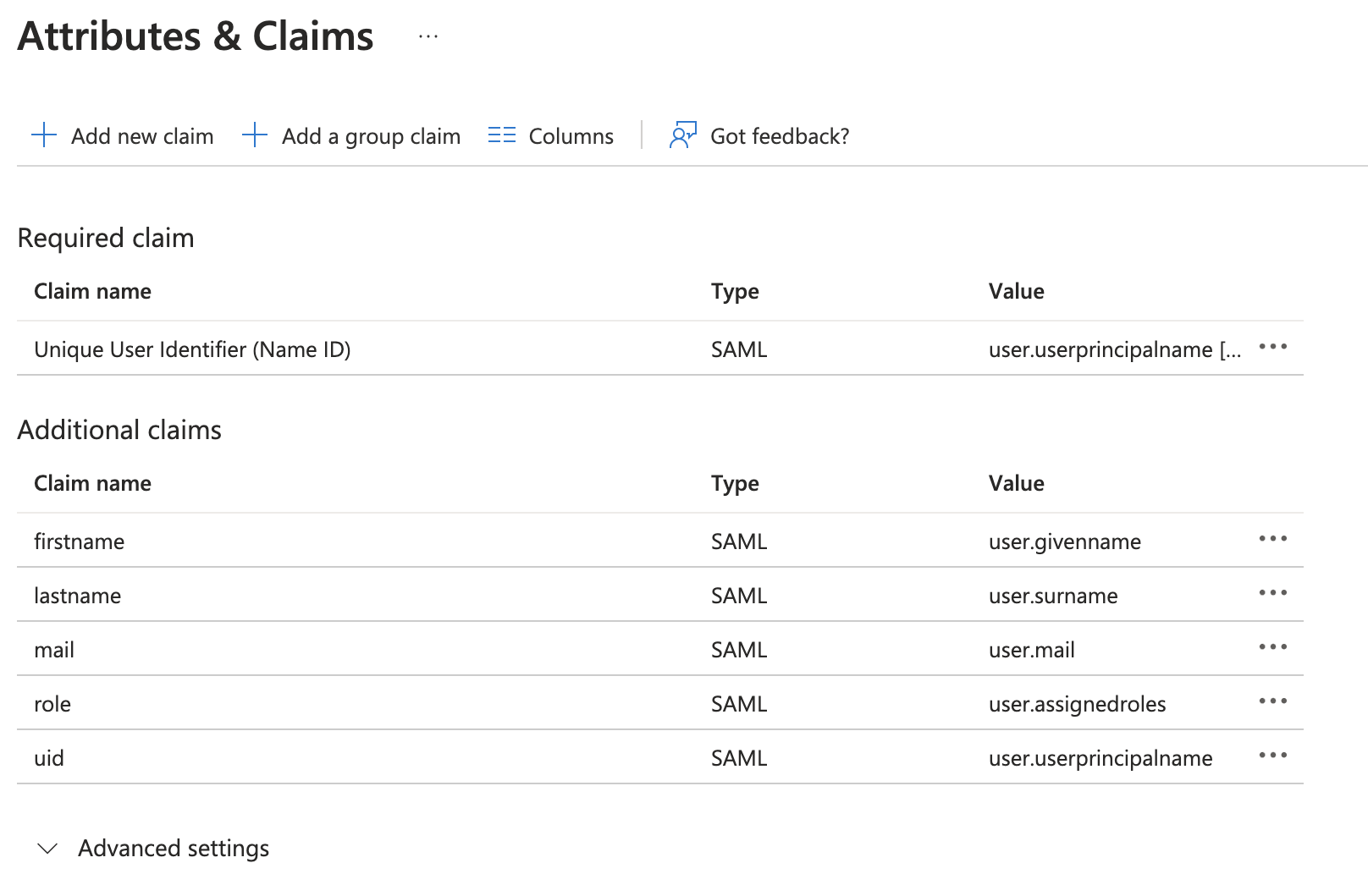
Configuring Attributes and Claims in Entra ID
-
For each claim, delete the Namespace value in the configuration.
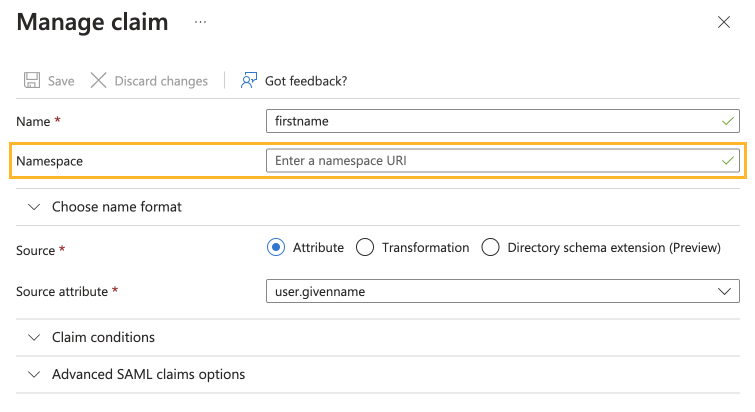
Leaving the "Namespace" Value Blank in the Claim Configuration
Manage role attribute
Create role attribute
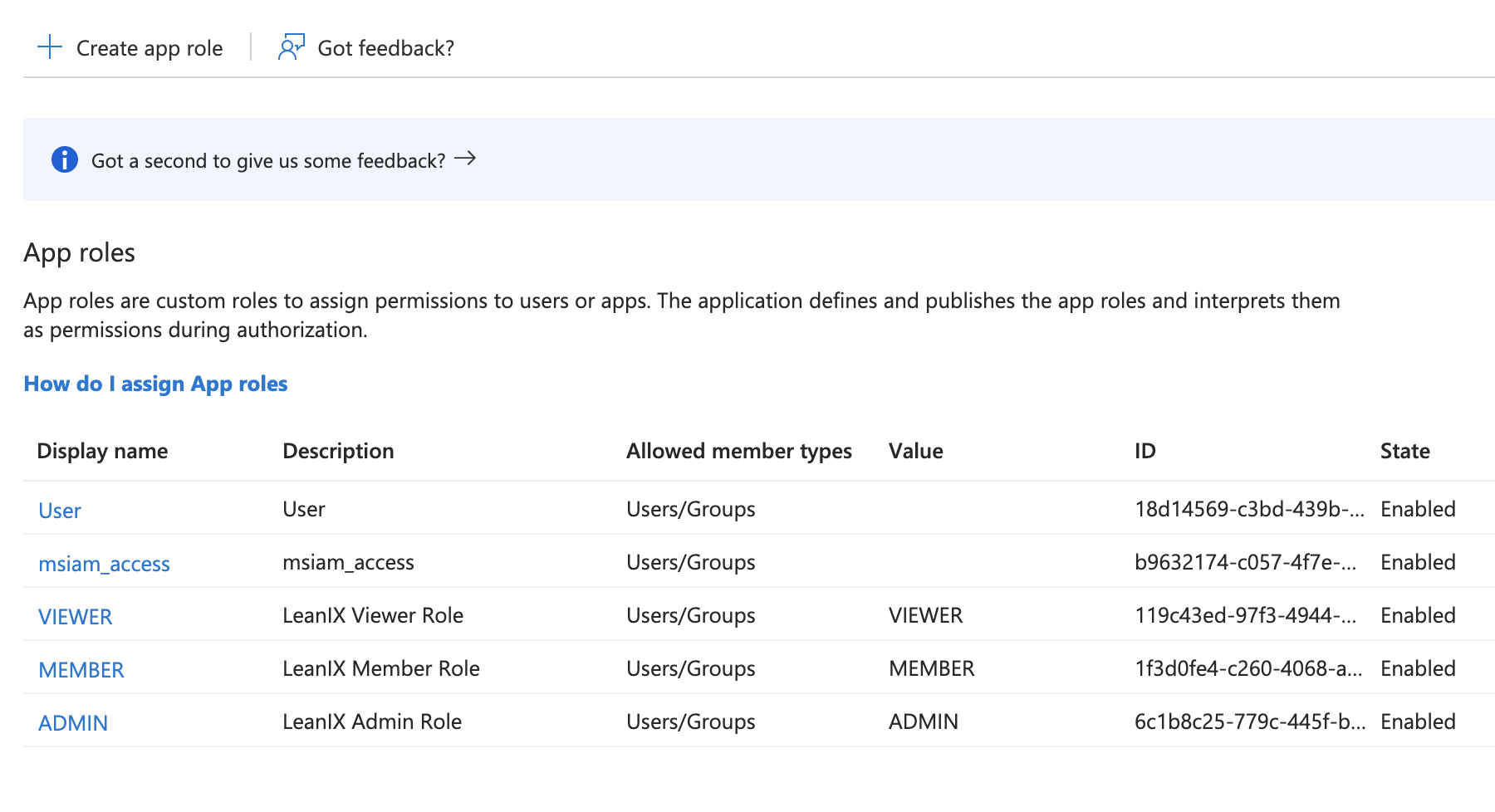
For customers who assign roles in Entra ID, it's necessary to create corresponding App Roles in your App Registrations.
Assign role attribute
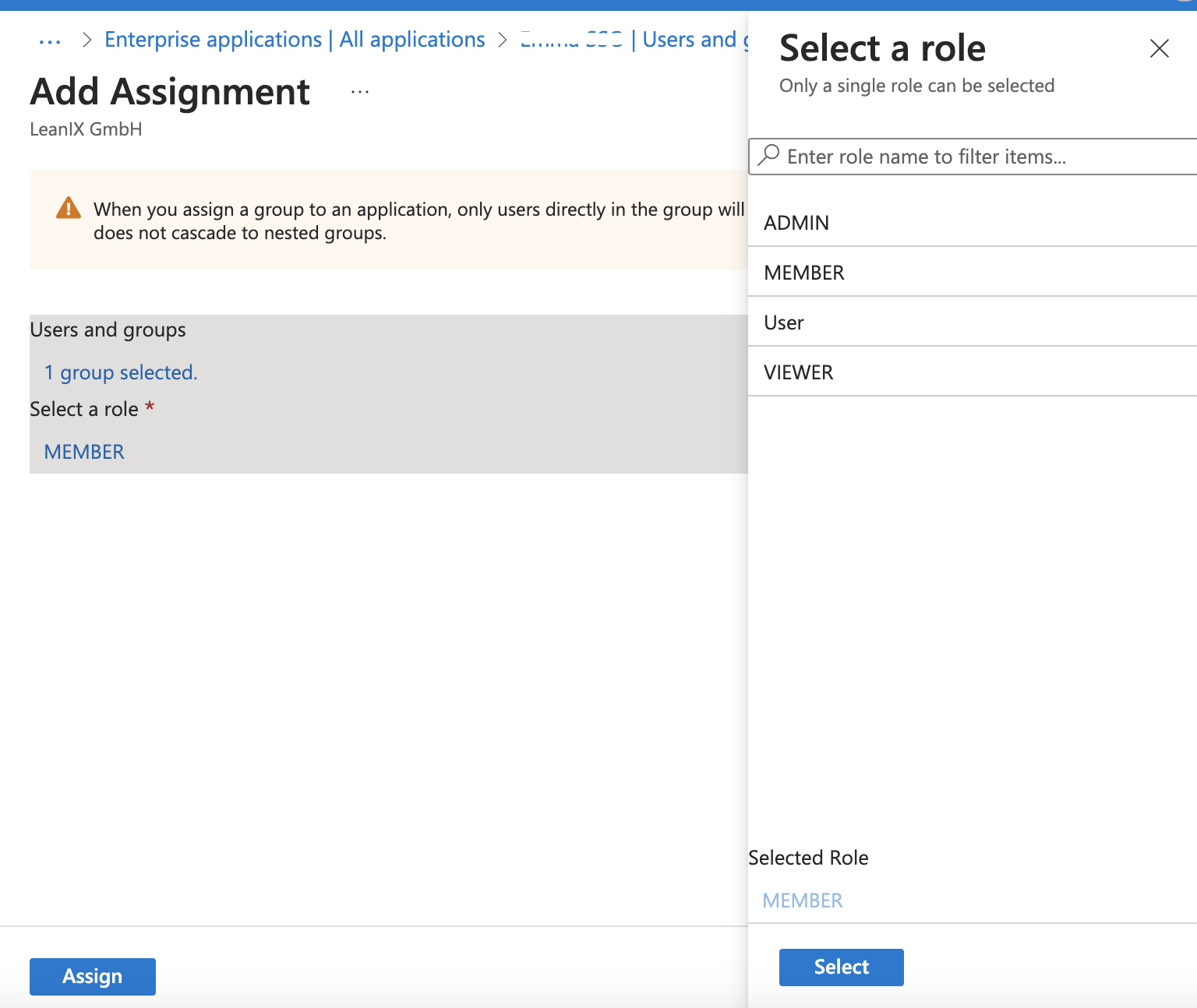
These app roles can then be assigned to users and/or groups within the enterprise application.
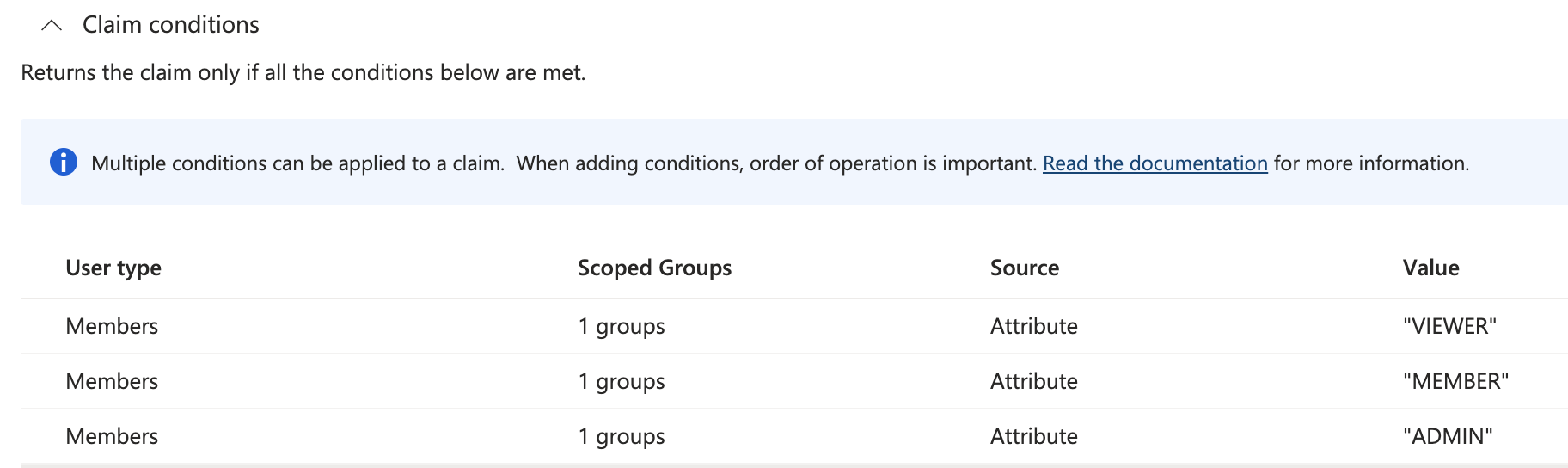
Claim Conditions
Claim conditions are an option for assigning roles to Active Directory groups. When adding conditions, they will be met in order of appearance. In the example below, if a user belongs to scoped groups of "VIEWER" and "MEMBER," they will be assigned VIEWER permission by order of operation.
To learn how to configure the user.assignedroles values, please refer to the Entra ID documentation.
Updated 3 days ago
